In today’s fast-evolving threat landscape, cyber security professionals need reliable, secure hardware to handle sensitive tasks like penetration testing, threat analysis, and secure remote access. A secure mini PC offers the perfect balance of power, portability, and protection in a compact form factor. Whether you’re setting up a dedicated lab machine, a travel companion for conferences, or a home workstation for ongoing monitoring, knowing how to setup secure mini pc for cyber security professionals is essential.
This guide is designed for professionals who demand enterprise-grade security without the bulk of traditional desktops. We’ll cover everything from hardware selection emphasizing features like TPM 2.0 and secure boot, to software hardening and network isolation. If you’re new to mini PCs or looking to upgrade your setup, this is your roadmap to a fortress-like system.
Check out our blog for more insights on cybersecurity hardware trends and best practices in 2026.

Preparation
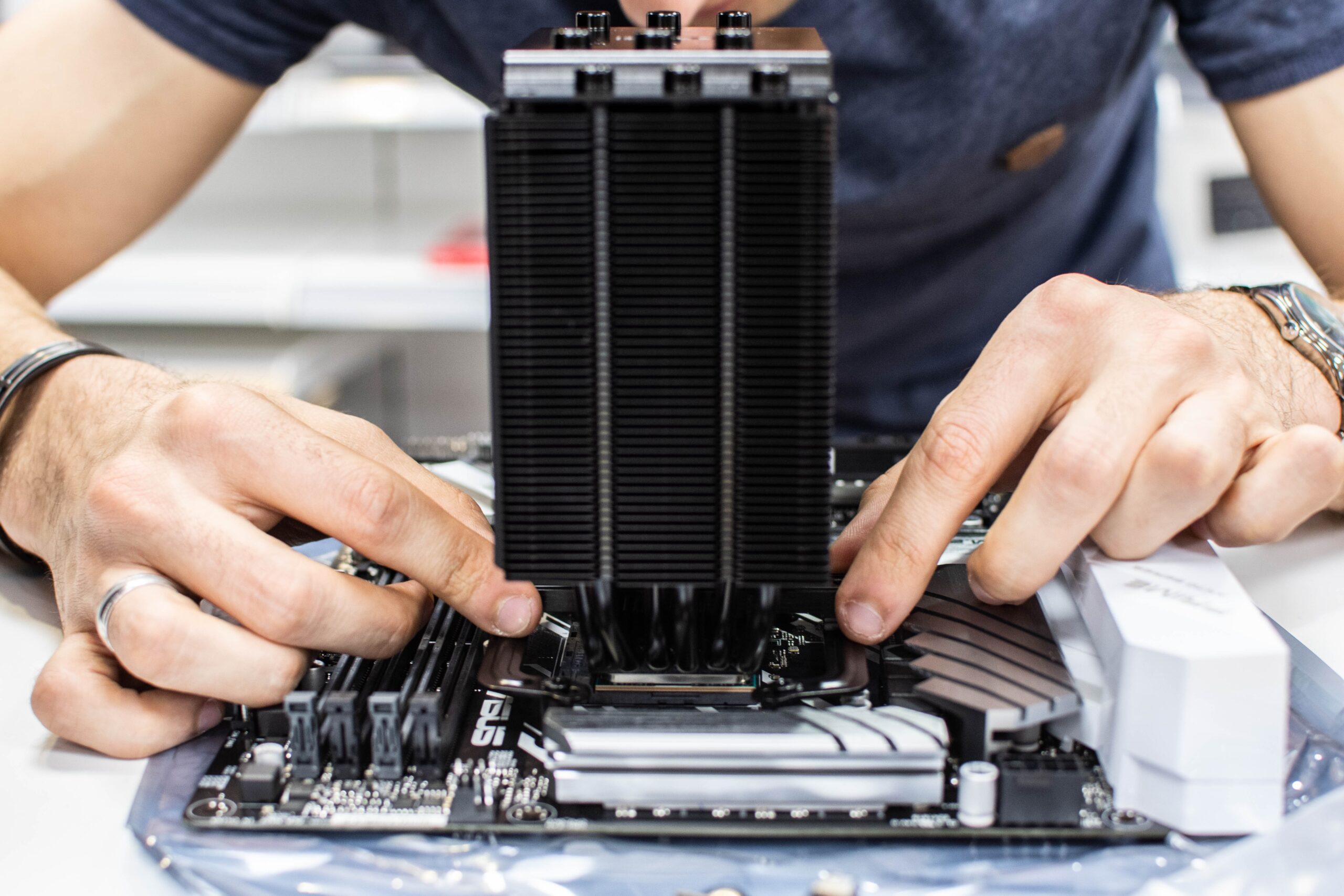
Before diving into the setup, gather the right components to build a robust foundation. Start with a mini PC featuring Intel Core or AMD Ryzen processors (12th gen or newer), at least 16GB DDR5 RAM, and a 512GB NVMe SSD for fast, encrypted storage. Ensure it supports TPM 2.0 for hardware-based security and has multiple USB ports, HDMI, and Wi-Fi 6E for connectivity.
Software-wise, download the latest ISO for a security-focused OS like Ubuntu LTS or Fedora, which offer built-in SELinux and AppArmor. You’ll also need a USB bootable drive (at least 16GB), an external monitor/keyboard/mouse for initial setup, and backups of any data. Verify BIOS/UEFI settings accessibility and have your product keys ready. We recommend testing hardware integrity with tools like MemTest86 beforehand.
- Hardware: Mini PC with TPM 2.0, secure boot, DDR5 RAM, NVMe SSD
- Software: Linux distro ISO, Rufus for bootable USB, VeraCrypt for encryption
- Tools: Ethernet cable for initial wired connection, YubiKey for 2FA
Step-by-Step Setup Guide
Follow these 8 detailed steps to transform your mini PC into a secure powerhouse. Each step includes tips and warnings to avoid common pitfalls.
- Enter BIOS/UEFI and Enable Security Features: Power on and press Del, F2, or F10 to enter setup. Enable TPM 2.0, Secure Boot, and disable legacy boot. Set a strong supervisor password. Tip: Prioritize UEFI mode for modern security. Warning: Note your changes; forgetting the password locks you out.
- Create Bootable USB and Install OS: Use Rufus to make a bootable USB from your Linux ISO. Boot from USB, select full disk encryption during install (LUKS). Choose a strong passphrase. Tip: Allocate 100GB+ for root partition. Warning: Backup data first—installation wipes the drive.
- Post-Install Updates and Hardening: Boot into the OS, run
sudo apt update && sudo apt upgrade(Ubuntu). Install kernel hardening tools like auditd. Enable firewall with UFW:sudo ufw enable. Tip: Reboot after updates. - Configure User Accounts and Authentication: Create a non-root user with sudo privileges. Set up 2FA with Google Authenticator or YubiKey via PAM. Disable root login over SSH. Tip: Use
passwdfor strong policies. - Implement Full Disk and File Encryption: If not done during install, use VeraCrypt for containers or LUKS for volumes. Encrypt sensitive directories. Tip: Test decryption speed on NVMe SSD.
- Secure Networking and Firewall Rules: Connect via Ethernet first. Configure VPN (WireGuard or OpenVPN) for all traffic. Set UFW rules: deny inbound except SSH/VPN on specific ports. Enable Wi-Fi 6E with WPA3. Tip: Use
ufw status verboseto verify. - Install Cyber Security Tools: Add Wireshark, Nmap, Metasploit, Snort IDS, and ClamAV. Containerize with Docker for isolation. Tip: Use flatpak for sandboxed apps.
- Test and Verify Security: Run Lynis or OpenVAS scans. Test boot integrity and penetration attempts. Monitor with
journalctl. Tip: Automate daily scans via cron.
Optimization Tips
Take your setup further with these practical optimizations for peak performance and security.
- Enable AppArmor/SELinux profiles for all services to confine processes.
- Schedule automatic snapshots with Timeshift for quick restores.
- Use ZFS or Btrfs filesystems for built-in checksumming and compression on NVMe SSDs.
- Implement fail2ban to block brute-force attacks on SSH.
- Offload AI tasks to NPU if available, or add eGPU for GPU-accelerated cracking tools.
- Monitor temperatures with lm-sensors; undervolt CPU for efficiency in compact chassis.
- Regularly rotate keys and certs; use Keybase or age for file encryption.
Troubleshooting
Encounter issues? Here’s how to resolve common problems:
- Boot Failure: Check Secure Boot compatibility; disable temporarily to test ISO.
- Encryption Unlock Issues: Boot to recovery mode and chroot to reset passphrase.
- Network Blocks: Review UFW logs with
sudo ufw status logged; allow ports as needed. - Overheating: Ensure vents are clear; repaste thermal compound on CPU.
- Tool Crashes: Update dependencies; use virtual environments with venv.
Final Thoughts
Setting up a secure mini PC empowers cyber security professionals with a portable, high-performance machine ready for any challenge. By focusing on hardware like TPM 2.0 and DDR5, combined with hardened Linux configs, you’ll have a system that’s resilient against threats. Regularly update and audit your setup to stay ahead. We hope this guide helps you build confidence in your cybersecurity toolkit—start today and elevate your workflow!
FAQs
What OS is best for a secure mini PC?
Linux distributions like Ubuntu or Fedora with full disk encryption and SELinux are ideal for cyber pros due to their robust security features.
Do I need TPM 2.0 for cybersecurity work?
Yes, TPM 2.0 enables secure boot, disk encryption keys, and attestation, making it crucial for professional setups.
How often should I update my secure mini PC?
Weekly for security patches, monthly for full system upgrades to patch vulnerabilities promptly.
Can I use Windows for this setup?
Possible with BitLocker and Windows Defender, but Linux offers better control and fewer telemetry concerns.
Is a mini PC powerful enough for Metasploit?
Absolutely—with 32GB RAM and Ryzen CPU, it handles exploits, scanning, and analysis smoothly.





Write Your Review
No reviews yet. Be the first to share your experience!